I found a way to upgrade to the Enterprise plan without paying for it. The API trusted whatever plan name I sent. No verification. No extra charge.
How I Found It
I was testing a SaaS platform that offers different subscription tiers. They have Free, Pro, and Enterprise plans. Enterprise is the expensive one with all the features.
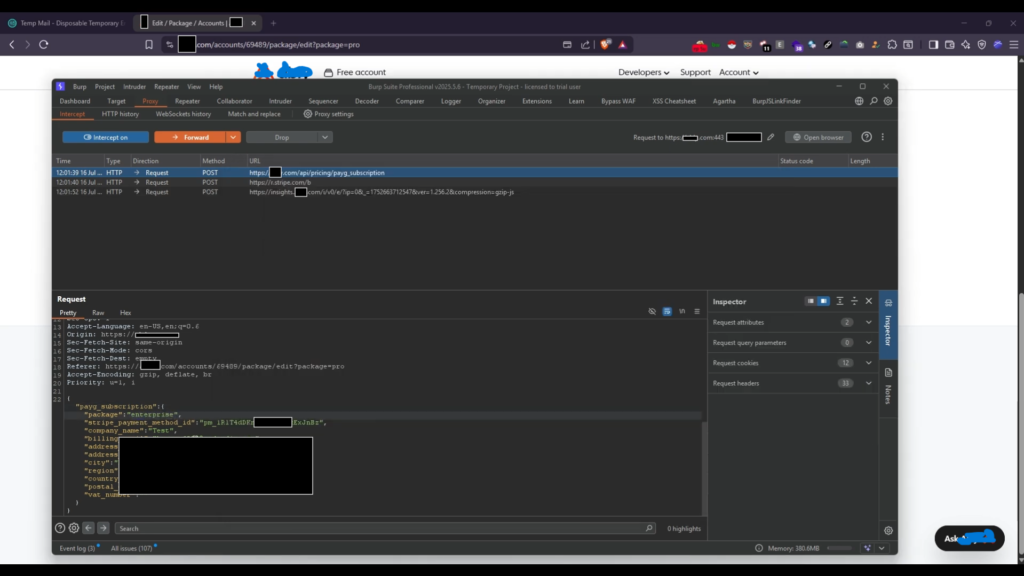
I signed up for the Pro plan and went through the payment process. Before submitting the final request, I intercepted it with Burp Suite.
The Request
The signup request looked like this:
POST /api/pricing/payg_signup
Content-Type: application/jsonjson
{
"package": "pro",
"name": "[REDACTED]",
"email": "[REDACTED]",
"stripe_payment_method_id": "[REDACTED]",
"company_name": "[REDACTED]",
"billing_email": "[REDACTED]",
"address_1": "[REDACTED]",
"city": "[REDACTED]",
"country_code": "[REDACTED]",
"postal_code": "[REDACTED]",
"accepts_terms": "1"
}I noticed the package parameter. It was set to pro because that’s what I selected.
I changed one word:
{
"package": "enterprise",
...
}Forwarded the request. It worked.
I refreshed my dashboard. My account was now on the Enterprise plan. I paid for Pro pricing but got Enterprise features.
No approval needed. No sales call. No extra payment.
The backend trusts the client. When you submit the form, the server takes whatever package value you send and assigns it to your account.
There’s no check like:
- Did the user actually pay for this plan?
- Is this plan available for self-signup?
- Does the payment amount match the selected plan?
The server just accepts it.
What an Attacker Can Do
- Sign up for the cheapest paid plan
- Change the package value to the most expensive tier
- Get premium features without paying
For this platform, Enterprise includes things like:
- Higher API limits
- Priority support
- Advanced integrations
- Features not available on lower tiers
An attacker could also sell “cheap Enterprise accounts” to others.
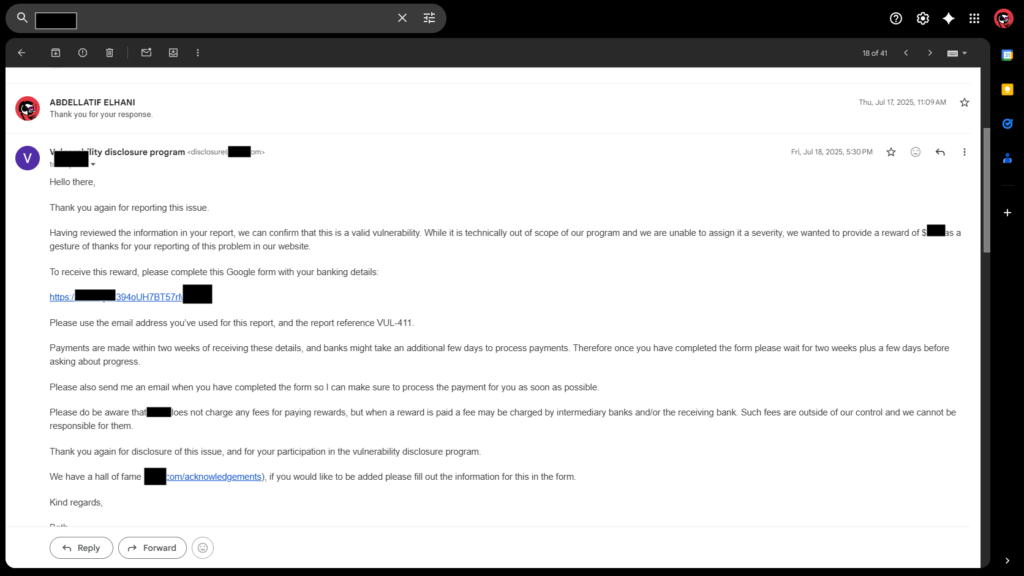
FOUND DATE: JUL 16, 2025