In this write up, I will show you how I found hardcoded MongoDB credentials in a public GitHub repository. The credentials were valid and granted me read access to 14 databases containing sensitive data.
What I Found
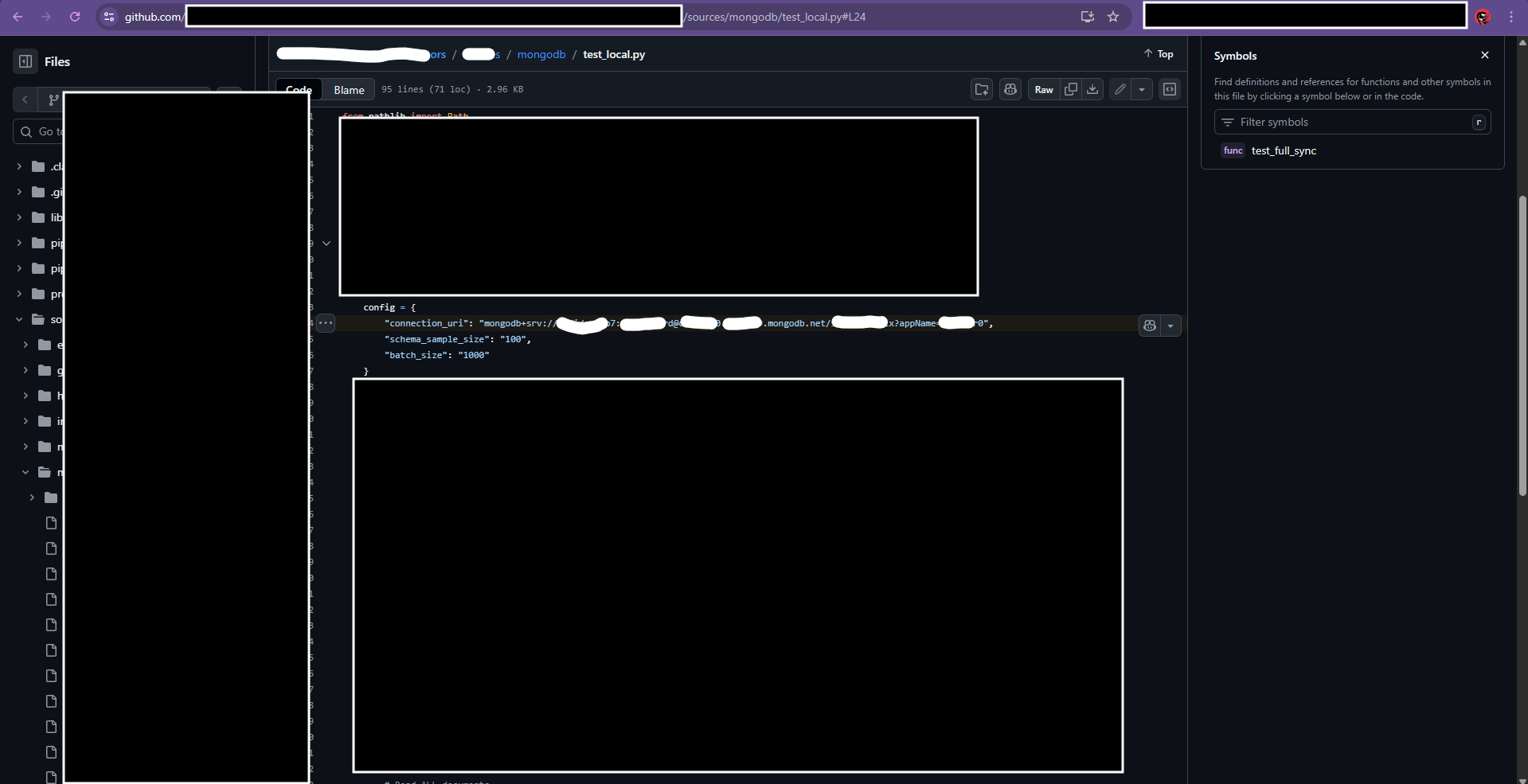
I was doing my regular GitHub reconnaissance when I found a Python test file with hardcoded MongoDB credentials. The file was called test_local.py And the credentials were sitting right there on line 24.
The connection string looked like this:
config = {
"connection_uri": "mongodb+srv://[REDACTED]:[REDACTED]@[REDACTED].mongodb.net/[REDACTED]",
"schema_sample_size": "100",
"batch_size": "1000"
}A developer committed this file with real username and password. Big mistake.
Testing the Credentials
First, I needed to check if the credentials were still valid. I used mongosh (MongoDB Shell) to connect:
mongosh "mongodb+srv://[USERNAME]:[PASSWORD]@[CLUSTER].mongodb.net/"And boom – I was in:
Current Mongosh Log ID: [REDACTED]
Connecting to: mongodb+srv://<credentials>@[REDACTED].mongodb.net/
Using MongoDB: 8.0.17
Using Mongosh: 2.5.10Connection successful. Now let’s see what we have access to.
What Was Exposed
I ran show dbs to list all databases:
[database_1] 72.00 KiB
[database_2] 252.00 KiB
[database_3] 56.68 MiB
[database_4] 14.55 MiB
[database_5] 1.98 MiB
[database_6] 72.00 KiB
[database_7] 115.63 MiB
[database_8] 11.89 MiB
[database_9] 2.02 MiB
[database_10] 65.57 MiB
[database_11] 4.31 MiB
[database_12] 216.00 KiB
admin 392.00 KiB
local 3.48 GiB14 databases. Some of them had sensitive names that suggested they contained real user data and financial records.
I checked the collections in one database:
comments
embedded_movies
movies
sessions
theaters
usersThe users collection caught my attention. This could contain PII (personal information) like emails and names.
I counted the documents:
db.movies.countDocuments()
# Result: 21357Over 21,000 documents in just one collection. I did a quick findOne() to confirm I could read the data, and yes – full documents were returned with all fields.
I stopped testing here and reported the issue immediately.
This leak is serious. Here’s what an attacker could do:
- Read all data from 14 databases
- Steal user information from the users collection (emails, names, etc.)
- Access financial data from databases that looked like they contained donation records
- Download everything – over 21,000+ documents without any authentication
All because someone committed a test file with real credentials.
FOUND DATE: Jan 16, 2026