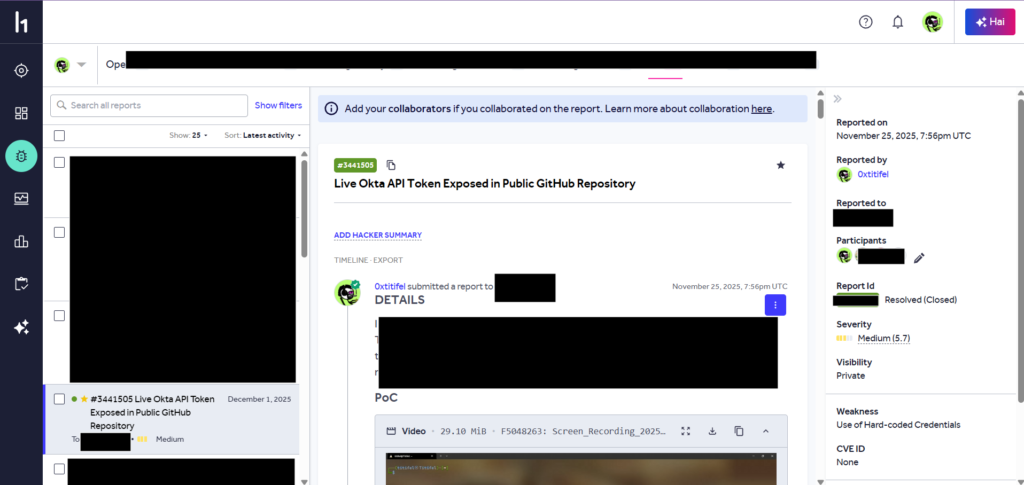
I found a working Okta API token in a public GitHub repository. The token was in a config file and it was still active. I tested it and got access to user data.
The Find
I was going through a public repo when I saw a JSON config file. Inside, there was an Okta API token and domain:
{
"auth.token": "[REDACTED]",
"domain": "[REDACTED].oktapreview.com"
}Plain text. No protection. Anyone can see it.
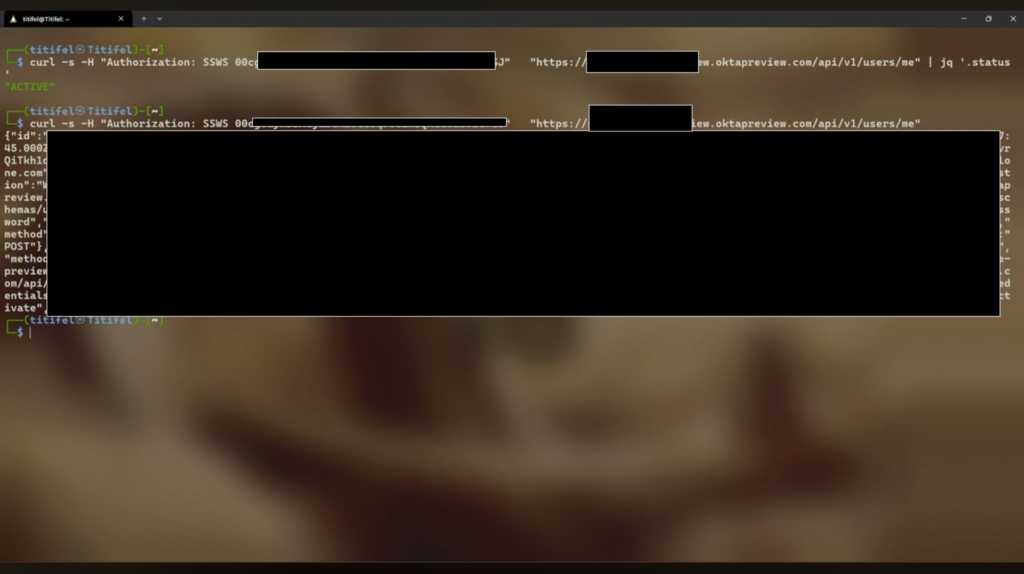
Testing It
I ran a simple curl to check if the token works:
curl -s -H "Authorization: SSWS [REDACTED]" \
"https://[REDACTED].oktapreview.com/api/v1/users/me"It worked. The API returned the full profile of a service account:
{
"id": "[REDACTED]",
"status": "ACTIVE",
"created": "2022-09-06T20:11:52.000Z",
"lastLogin": "2025-06-20T17:02:17.000Z",
"profile": {
"firstName": "[REDACTED]",
"lastName": "API Service",
"email": "[REDACTED]@[REDACTED].dev"
},
"_links": {
"suspend": { "href": "...", "method": "POST" },
"resetPassword": { "href": "...", "method": "POST" },
"deactivate": { "href": "...", "method": "POST" },
"changePassword": { "href": "...", "method": "POST" }
}
}The token was valid. The lastLogin showed it was used recently. And the _links section showed what actions are possible with this token.
What This Token Can Do
Based on the API response, this token can:
- View user accounts
- Suspend users
- Reset passwords
- Deactivate accounts
- Change security settings
This is an Okta admin token. It has access to identity management functions.
Why It Matters
Okta manages user identities. Companies use it for login, SSO, and access control. A leaked Okta token means someone can:
- See all users in the system
- Lock people out of their accounts
- Reset passwords and take over accounts
- Change security policies
Timeline
- Found the token in a public repo
- Tested it to confirm it was active
- Reported it to the security team
- Token was revoked
FOUND DATE: Nov 25, 2025